The safe cloud stable & secure
When it comes to safe cloud computing, businesses want to trust their cloud partner. That is why we do everything we can to ensure the Tilaa Cloud's security.
When it comes to safe cloud computing, businesses want to trust their cloud partner. That is why we do everything we can to ensure the Tilaa Cloud's security.
Tilaa places great importance on data security and data sovereignty. We are convinced that personal data, as well as data in a business context, is valuable. That is why we ensure quality and safety by certifying our processes and services in accordance with internationally recognized standards.
Our entire set of processes and procedures is monitored, evaluated, and improved continuously. Our users can be confident that we are constantly developing our services in order to maintain quality and safety.
In the field of IT service management and information security, we comply with ISO 27001, ISO/IEC 9001 and PCI DSS.
Your data is important and should never be up for grabs. To safeguard against this, Tilaa has acquired the ISO 27001 certification. ISO 27001 specifies standards for the implementation of security measures and audit mechanisms.
The infrastructure provided by Tilaa can be used as a foundation for a credit card processing platform. Even when you use the Tilaa platform for different purposes, this standard ensures a high level of security. A perfect addition to ISO 27001.
Tilaa is working continuously to improve customer satisfaction levels. With the ISO 9001 certification we have secured this process firmly in our organisation and with some great results: 98% of our customers would recommend Tilaa to others.
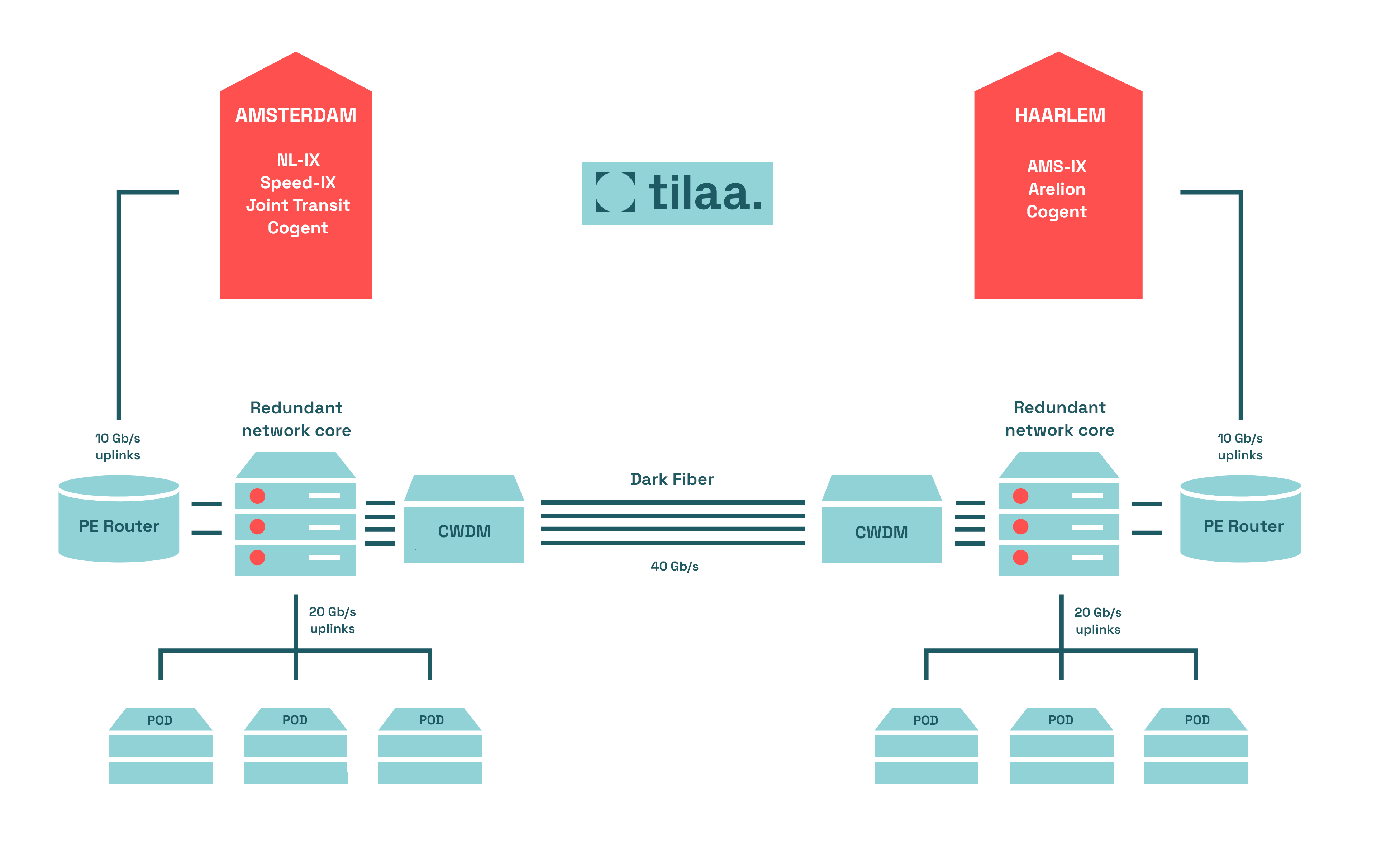
The Tilaa network (AS196752) uses multiple TIER-1 network suppliers (Cogent and Telia Company) and is directly connected to one of the largest internet exchanges in the world (AMS-IX). Therefore Tilaa has fast and redundant connections to all networks worldwide.
Our physical servers are connected with 2 patches to different rack switches. The rack switches are connected to the fully redundant core network. The various datacenter locations are connected using multiple dark fibers traversing different physical paths.
Our working methods, policies and procedures are designed to keep data leaks to a minimum.
By implementing strict access controls, conducting regular security audits and training all employees in security best practices, we create a secure environment that protects both our data and that of our users.
All Tilaa infrastructure is located within the borders of the European Union (EU). There are no direct connections to environments outside the Netherlands or Europe and ours are only accessible via a Dutch internet node.
All data hosted on our platform is protected by the Data Protection Directive of the EU, which regulates the processing of personal data. It is an important component of EU privacy and human rights law.
DDoS attacks are deliberate attempts by hackers to disrupt the traffic of a server, service, or network by overloading the target or surrounding infrastructure with non-legitimate (or seemingly genuine) data. The goal is to disrupt or possibly totally take down the service in issue, preventing people from using it (normally).
De you want to know how your business can prevent and respond to DDoS attacks?